Start your day with intelligence. Get The OODA Daily Pulse.
Start your day with intelligence. Get The OODA Daily Pulse.
Home > Example Query Loops
Exponential innovation is causing exponential disruption
Exponential innovation is causing exponential disruption
Exponential innovation is causing exponential disruption
In recent years, the U.S. government has intensified its efforts to hold companies accountable for cybersecurity failures, underscored by high-profile cases such as the prosecution of Uber’s former security chief, Joseph Sullivan, and the fallout from the SolarWinds breach. These actions send a strong message: American businesses entrusted with sensitive data must meet rigorous security standards. However, this new…
The CNAS “Secure, Governable Chips” report discusses using on-chip governance mechanisms to manage national security risks from AI and advanced computing to ensure secure, governable AI chip deployment.
The Future of Privacy Forum (FPF) recently released the report “Synthetic Content: Exploring Risks, Technical Approaches, and Regulatory Responses”, exploring the impact of synthetic media on trust, regulation, and the evolving digital landscape – including a fast-approaching future when, by 2026, online content generated by non-humans will vastly outnumber human-generated content
Insights from the CrowdStrike outage reveal critical lessons for board members and CISOs on enhancing collaboration, strategic thinking, and proactive cybersecurity measures.
Powering AI’s growth at double exponential speed will require navigating the immense energy demands of expanding data centers and understanding their impact on the global energy landscape—a crucial challenge for stakeholders in both AI and the energy sector.
The October 2024 OODA Network Monthly Meeting—held on Friday, October 18, 2024—featured guest speaker Dor Sarig, CEO & Co-founder of Pillar Security, to discuss the recently released Pillar Security report on The State of Attacks on GenAI.
The 2024 Geography of Crypto Report—an annual report from Chainalysis—provides an analysis of regional trends in cryptocurrency adoption and patterns crucial for investors, policymakers, and businesses as they navigate the evolving global landscape of crypto adoption.
Last week, the UK proposed a new data protection regime, hoping for an economic boost by hueing closer to EU data protection laws – while the U.S. proposed new rules governing data transfers to adversarial nations. Details here.
The government needs large clusters of GPUs dedicated to missions that matter to national security and acceleration of AI in service to our citizens. We currently have none.
The 2024 BRICS Summit in Kazan, Russia, featured 22 heads of state and delegations from over 30 countries. Key topics of the summit include further expansion of BRICS and the establishment of a new payment system for member countries—the beginnings of what some call the “de-dollarization” of the global economy and the strategic toppling of…

Allan Friedman is a senior strategist at CISA (the Cyber Security and Infrastructure Security Agency) where he coordinates all of their cross-sector activities on the topic of SBOM: The Software Bill of Materials.

Joe Sullivan has been at the forefront of managing security risk in rapidly growing high tech companies over the past 20 years serving as the Chief Security Officer at Facebook from early start-up through the IPO, CSO of Uber and CloudFlare, and as a security leader at eBay/PayPal. Learn what motivates him and some of…

Joe Tranquillo is a Professor of Biomedical Engineering at Bucknell University and a provost at the school. He is also and author and speaker with a knack for helping make new and at times complex subjects understandable. In this OODAcast we discuss many aspects of the revolution in biological sciences with Joe including topics like:…

Charles Clancy has successfully led technology efforts in government, industry, academia and continues to lead and innovate in his current position as Senior Vice President and GM of MITRE Labs. He is MITRE’s Chief Futurist. His role in technology leadership and his tracking of tech across multiple domains made for an incredibly insightful OODAcast. We…

Mark McGrath has applied the teachings of John Boyd to a career that began in the Marine Corps, included leadership positions in financial services firms and consulting with businesses with a need to learn to thrive in volatile, uncertain, complex and ambiguous (VUCA) environments. He co-founded the consultancy AGLX and serves as its Chief Learning…

Serene is a hacker in the truest sense of the word. She’s applied a hacker mindset to learn coding, piano, and blend art and engineering in fascinating ways. You’ll find her collaborating on-stage with Grimes one night and coding censorship resistant technologies the next day. As a self-taught coder she was the first engineer hired…
Andy Bochman is the Senior Grid Strategist-Defender for Idaho National Laboratory’s National and Homeland Security directorate. In this role, Andy provides strategic guidance on topics at the intersection of grid security and climate resilience to INL leadership as well as senior U.S. and international government and industry leaders. Andy is a frequent speaker, writer, and trainer…
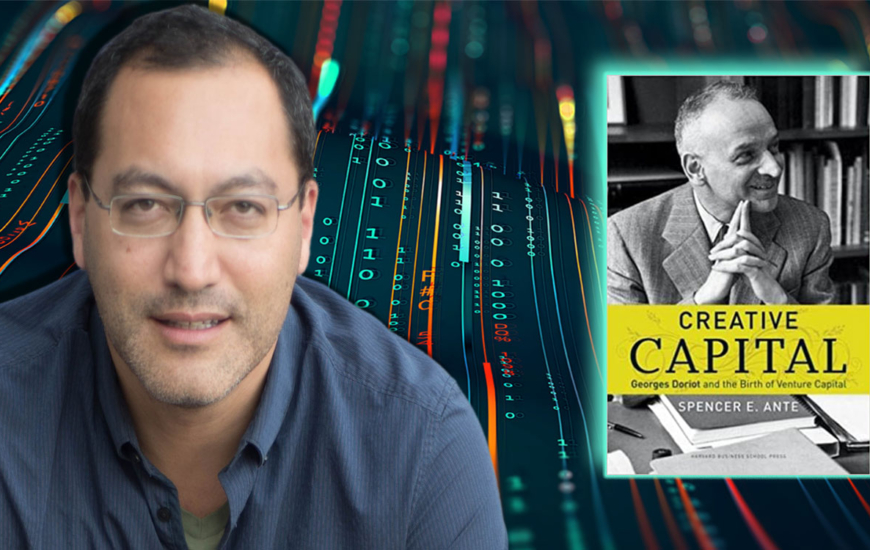
Spencer Ante is the author or “Creative Capital: Georges Doriot and the Birth of Venture Capital”, which was on my Top 10 book list for 2022. In fact, I found Doriot’s story so compelling that a portrait of him hangs on the wall at the Hack Factory start-up studio in Reston, VA. Doriot is a…

Bob Zukis is a man on a mission to improve the ability of corporate America to succeed in a complex digital world, even when under constant cyber attack. Bob is the CEO and founder of the Digital Directors Network, the global pioneer in helping corporate directors advance their understanding of systemic risk. We consider Bob…
Adam Shostack is widely known in the cybersecurity world for his pioneering work on disclosing and discussing computer vulnerabilities (the CVE (common vulnerabilities and exposures) list). He also helped formalize and train leading approaches to threat modeling and wrote the foundational book on the subject (Threat Modeling: Designing for Security). In this OODAcast we seek…
Copyright © 2025 — All Rights Reserved.
Notifications
