Start your day with intelligence. Get The OODA Daily Pulse.
Start your day with intelligence. Get The OODA Daily Pulse.
Home > Example Query Loops
Exponential innovation is causing exponential disruption
Exponential innovation is causing exponential disruption
Exponential innovation is causing exponential disruption
Recent reporting has revealed that China appears interested in exploiting recent cuts made by the Department of Government Efficiency (DOGE) to the U.S. federal workforce by targeting individuals that have been let go with promises of employment in the hopes of obtaining classified information. According to a researcher from a Washington, D.C.-based think tank, Chinese intelligence has allegedly…
The AI business landscape is shifting from a focus solely on innovation capacity to an emphasis on diffusion capacity, recognizing that the ability to scale AI applications is more valuable than standalone technological breakthroughs. Many companies invest heavily in research but struggle with widespread adoption, leading to underutilized advancements.
This New York Deep Tech Week 2025 panel will discuss how emerging technologies, such as AI-powered cyber warfare, quantum-secured communications, and autonomous battle networks, redefine national security. OODA and the OODA Network are your hosts for this discussion.
The national security mission could use some help. The nation has a huge need for advanced technologies that can improve defense and intelligence capabilities.
As AI becomes more deeply embedded in national security, enterprise infrastructure, and everyday tools, the debate over open-source vs. closed-source models is no longer academic—it’s geopolitical. In a recent OODA Network discussion, Mike Sexton of Third Way outlined why open-source AI must be treated as a strategic priority for the United States.
The recent U.S. AI policy reversals aside: the AI technology diffusion model should remain central to your AI business strategy (i.e. customer development, vendor relationships, strategic partnerships, business model generation, value proposition design, and platform economics).
Selling to government agencies requires navigating a labyrinth of regulations, compliance requirements, and acquisition processes, all while aligning your solution with both shifting political priorities and mission objectives.
This week’s member only OODA network dispatch provides insights into some of the dramatic changes underway in US and Chinese robotics and AI capabilities as well as an update on the geopolitical dynamics set off by the trade war. We held our March member meeting video call today. Topic was federal government spending on AI. We…
Researchers at the Center for Security and Emerging Technology (CSET) continue to build on their March 2024 “Argument for Hybrid AI Incident Reporting” with a mandatory AI incident reporting framework designed to systematically capture harms from artificial intelligence systems.
The Annual Threat Assessment of the U.S. Intelligence Community, released annually by the Office of the Director of National Intelligence (ODNI), highlights the most pressing threats facing the United States.

Allan Friedman is a senior strategist at CISA (the Cyber Security and Infrastructure Security Agency) where he coordinates all of their cross-sector activities on the topic of SBOM: The Software Bill of Materials.

Joe Sullivan has been at the forefront of managing security risk in rapidly growing high tech companies over the past 20 years serving as the Chief Security Officer at Facebook from early start-up through the IPO, CSO of Uber and CloudFlare, and as a security leader at eBay/PayPal. Learn what motivates him and some of…

Joe Tranquillo is a Professor of Biomedical Engineering at Bucknell University and a provost at the school. He is also and author and speaker with a knack for helping make new and at times complex subjects understandable. In this OODAcast we discuss many aspects of the revolution in biological sciences with Joe including topics like:…

Charles Clancy has successfully led technology efforts in government, industry, academia and continues to lead and innovate in his current position as Senior Vice President and GM of MITRE Labs. He is MITRE’s Chief Futurist. His role in technology leadership and his tracking of tech across multiple domains made for an incredibly insightful OODAcast. We…

Mark McGrath has applied the teachings of John Boyd to a career that began in the Marine Corps, included leadership positions in financial services firms and consulting with businesses with a need to learn to thrive in volatile, uncertain, complex and ambiguous (VUCA) environments. He co-founded the consultancy AGLX and serves as its Chief Learning…

Serene is a hacker in the truest sense of the word. She’s applied a hacker mindset to learn coding, piano, and blend art and engineering in fascinating ways. You’ll find her collaborating on-stage with Grimes one night and coding censorship resistant technologies the next day. As a self-taught coder she was the first engineer hired…
Andy Bochman is the Senior Grid Strategist-Defender for Idaho National Laboratory’s National and Homeland Security directorate. In this role, Andy provides strategic guidance on topics at the intersection of grid security and climate resilience to INL leadership as well as senior U.S. and international government and industry leaders. Andy is a frequent speaker, writer, and trainer…
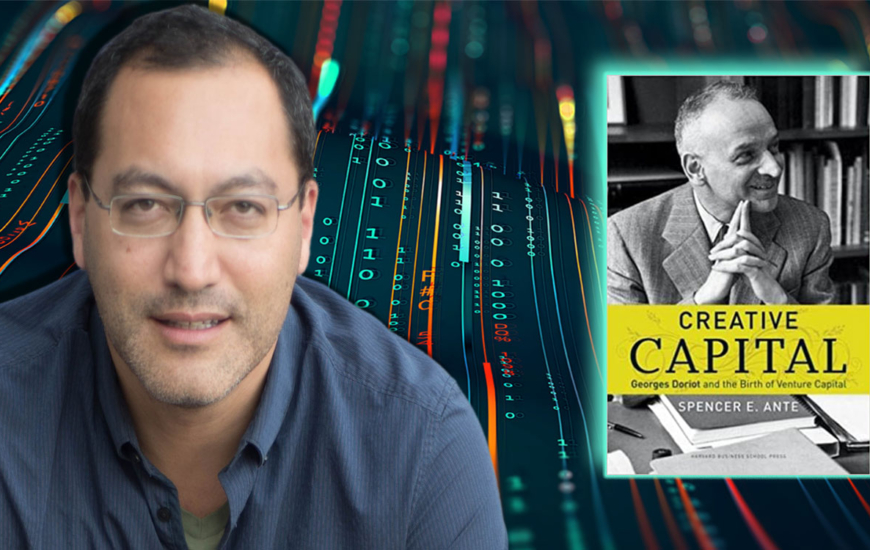
Spencer Ante is the author or “Creative Capital: Georges Doriot and the Birth of Venture Capital”, which was on my Top 10 book list for 2022. In fact, I found Doriot’s story so compelling that a portrait of him hangs on the wall at the Hack Factory start-up studio in Reston, VA. Doriot is a…

Bob Zukis is a man on a mission to improve the ability of corporate America to succeed in a complex digital world, even when under constant cyber attack. Bob is the CEO and founder of the Digital Directors Network, the global pioneer in helping corporate directors advance their understanding of systemic risk. We consider Bob…
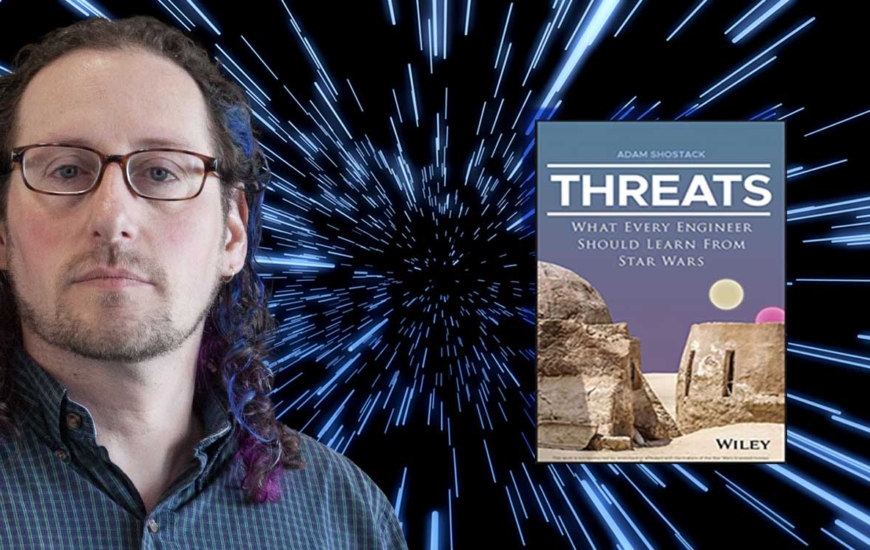
Adam Shostack is widely known in the cybersecurity world for his pioneering work on disclosing and discussing computer vulnerabilities (the CVE (common vulnerabilities and exposures) list). He also helped formalize and train leading approaches to threat modeling and wrote the foundational book on the subject (Threat Modeling: Designing for Security). In this OODAcast we seek…
Copyright © 2025 — All Rights Reserved.
Notifications
